& meet dozens of singles today!
User blogs
On the day a violent mob of Trump supporters stormed the U.S. Capitol, a worried GitHub employee warned his co-workers in the D.C. area to be safe.
After making a comment in Slack saying, “stay safe homies, Nazis are about,” a fellow employee took offense, saying that type of rhetoric wasn’t good for work, the former employee told me. Two days later, he was fired, with a human relations representative citing a “pattern of behavior that is not conducive to company policy” as the rationale for his termination, he told me.
In an interview with TechCrunch, the now-former employee said he was genuinely concerned about his co-workers in the area, in addition to his Jewish family members.
TechCrunch agreed to keep the identity of the terminated employee confidential due to fears of his and his family’s safety.
As Business Insider first reported, his firing led to employees circulating an internal letter asking GitHub to denounce white supremacy and Nazis. The employees also wanted answers about his firing. That led to GitHub CEO Nat Friedman telling employees the company would investigate the termination of the employee.
Now, the terminated employee says he is currently seeking counsel to ensure his family is protected, as well as figure out if he can receive damages or some other form of reconciliation. The fired employee said GitHub has reached out to him for help in the internal investigation, but is waiting to engage with the company until he has legal representation in place.
Still, he said he is not optimistic about the investigation.
“I am 90% sure it’s not genuine,” the terminated employee said of Friedman’s response. “This type of stuff had been said before. It happened with the ICE stuff where the company said let’s have discussions but then if you mention ICE, you get fired. I used to believe in this company, but now I don’t.”
Similar to what some employees are asking, the terminated employee sees this as an opportunity for GitHub to take a stance on white supremacy.
He said, “I feel like this could be an opportunity for GitHub to really do a purge and say ‘Do we want white supremacists at this company and how do we get Black leaders into executive management?’
The latter is something he said he’s been asking for since he joined GitHUb. But as he kept talking about the lack of diversity at the leadership level, he said he found his job at risk.
“When I kept talking about it, I got threatened being fired in October,” he said. “Both my managers had to come completely to my defense and beg them not to fire me when I pointed out how the sales team maybe has just two people of color.”
In a blanket statement to TechCrunch about the contents of this article, a GitHub spokesperson said:
We take all complaints of this nature very seriously. We are actively investigating the situation.
Upon his termination, the former employee said the company gave him two paychecks and sent him on his way. He said he would be open to some form of reconciliation, whether in the form of damages, healthcare coverage or something else. While he’s not looking for his job back, he says he would like to see more worker power at GitHub.
“If I had a magic wand, I’d love for the employees at GitHub to be able to have a union and represent people from marginalized communities,” he said.
The United States’ GPS system, which is operated by the Defense Department, offers every one of us critical infrastructure around what is known as positioning, navigation and timing (PNT). Positioning and navigation is obvious every time we open up a maps app, but timing is also a critical function of GPS — offering our smartphones and devices precision timing to ensure that compute processes are accurately synced.
As more of the economy relies on these systems, they have increasingly become a target of hackers through GPS spoofing. The government wants to create additional redundancy and resiliency in the sector, and has explored using commercial alternatives to augment or backup parts of the GPS system.
The Department of Transportation, under a Congressional mandate added to the defense authorization bill for fiscal year 2018, ran a comprehensive evaluation of commercial alternatives to government-owned and operated GPS that could serve as a backup to our existing infrastructure.
Among the 11 companies considered in the study were a number of prominent positioning startups, including Satelles, which raised a $26 million round of capital in 2019; NextNav, which has raised a total of nearly $300 million including $120 million from Fortress a year ago; and Hellen Systems, which according to Crunchbase raised a small seed round last year.
You can read the full report from the DOT, which runs to 457 pages long and covers all 14 measures the researchers explored in evaluating these different PNT platforms.
The summary though is that there are a number of companies that offer decent backup capabilities for GPS, although the performance and cost vary widely. NextNav came out furthest ahead according to the researchers, who stated that “All [Technology Readiness Level]-qualified vendors demonstrated at least some PNT performance of value, but only one vendor, NextNav, demonstrated in all applicable use case scenarios.”
Beyond that, the DOT researchers said that “… none of the systems can universally backup the positioning and navigation capabilities provided by GPS and its augmentations.” Given the range of needs that GPS fulfills, they recommended that “a diverse universe of positioning and navigation technologies” be used to add resiliency in this infrastructure.
Finally, costs remain quite complicated to determine. Given the way that different positioning systems operate, the fixed and variable costs for each system are highly dependent on desired coverage area and necessary transmitter density. The researchers weren’t able to devise a clear opinion on the cost effectiveness of different systems, although they do offer some initial data that can provide early insight.
Given the importance of GPS and the desire for companies and the government to have reliable alternatives, VCs have dumped money on the PNT sector in recent years. Now, we have some hard data on which vendors are potentially picking up steam in terms of functionality and utility.
The dating and networking service Bumble has filed to go public.
The company, launched by a former co-founder of the IAC-owned Tinder, plans to list its share on the Nasdaq stock exchange, using the ticker symbol “BMBL.” Bumble’s planned IPO was first reported in December.
Bumble CEO Whitney Wolfe Herd was on the founding team at Tinder before starting Bumble. She filed suit against Tinder for sexual harassment and discrimination, which was at least somewhat inspirational in her quest to build a dating app that put women in the driver’s seat.
In 2019, Wolfe Herd took the helm of MagicLab, renamed to Bumble Group, in a $3 billion deal with Blackstone, replacing Badoo founder and CEO Andrey Andreev following a harassment scandal at the firm.
The company is targeting the public markets at a particularly heady time for new offerings, with investors embracing venture-backed IPOs throughout late 2020 and the start of 2021. Previously privately held companies like Airbnb, Affirm, and others have seen their fortunes soar on the back of prices that public investors are willing to pay, perhaps inducing more IPO filings than the market might have otherwise seen.
You can read its IPO filing here. TechCrunch will have its usual tear-down of the document later today, but we have pulled some top-line numbers for you to kick off your own research.
But before we do, the company’s board makeup, namely that it is over 70% women is already drawing plaudits. Now, into its numbers.
Inside Bumble’s IPO filing
Let’s consider Bumble from three perspectives: Usage, financial results, and ownership.
On the usage front, Bumble is popular, as you would imagine a dating would have to be to reach the scale required to go public. The company claims 42 million monthly active users (MAUs) as of Q3 2020 — many companies will try to get public on the strength of their third-quarter results from 2020, as it takes time to close Q4 and the full calendar year.
Those 42 million MAUs translated into 2.4 million total paying users through the first nine months of 2020; the percent, then, of paying users to MAUs is not 2.4 million divided by 42, but a smaller fraction.
Turning to the numbers, recall that Bumble sold a majority of itself a few years back. We bring that up as Bumble’s financial results are complicated thanks to its ownership structure.
After the IPO, Bumble Inc. will “be a holding company, and its sole material asset will be a controlling equity interest in Bumble Holdings,” per the S-1 filing. So, how is Bumble Holdings doing?
Medium? Doing the sums ourselves as the company’s S- 1 is fraught with accounting nuances, in the first nine months of 2019, Bumble managed the following:
- Revenues of $362.6 million
- Net income of $68.6 million
And then, combining two columns to provide a similar set of results for the same period of 2020, Bumble recorded:
- Revenues of $416.6 million
- Net income of -$116.7 million
For those following along, we’re using the “Net (loss) earnings” line, for profitability, and not the “Net (loss) earnings attributable to owners / shareholders” as that would require even more explanation and we’re keeping it simple in this first look.
While Bumble saw modest growth in 2020 through Q3 and a sharp swing to losses on a GAAP basis, the company’s adjusted profitability grew over the same time period. The company’s adjusted EBITDA, a very non-GAAP metric, expanded from $80.0 million in the first three quarters of 2019 to $108.3 million in the same period of 2020.
While we are generally willing to allow quickly-growing companies some leniency when it comes to adjusted metrics, the gap between Bumble’s GAAP losses and its EBITDA results is a stress-test of our compassion. Bumble also swung from free cash flow positivity during the first nine months of 2019 to the first quarters of 2020.
If you extrapolate Bumble’s Q1, Q2, and Q3 revenue to a full-year number, the company could manage $555.5 million in 2020 revenues. Even at a modest software-ish multiple, the company would be worth more than the $3 billion figure that we discussed before.
However, its sharp unprofitability in 2020 could damper its eventual valuation. More as we dig more deeply into the filing.
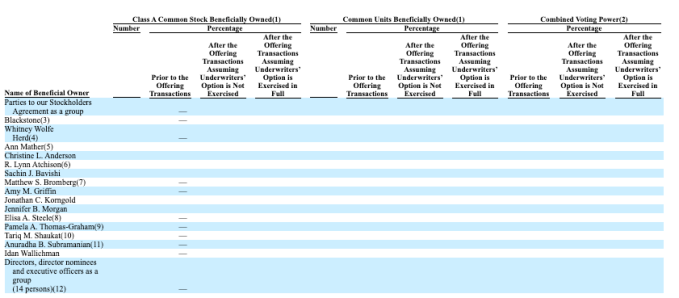
Finally, on the ownership question the company’s filing is surprisingly denuded of data. Its principal shareholder section looks like this:
When we know more, we’ll share more. Until then, happy S-1 reading.
Source: https://techcrunch.com/2021/01/15/bumble-files-to-go-public/
German startup Moss has raised a $25.5 million (€21 million) funding round led by Valar Ventures. Existing investors Cherry Ventures and Global Founders Capital are also participating. Moss provides credit cards and a spending platform to small and medium businesses in Germany.
The company has developed its own risk engine to come up with a credit card limit for your company. Like Brex in the U.S., Moss promises higher credit card limits compared to credit cards offered by traditional financial institutions.
Again, Moss doesn’t offer prepaid or debit cards — it focuses on credit cards. You can spend within your limits and pay at the end of the month. You don’t need to top up your Moss account to start using it.
Credit cards work on the Mastercard network. Admins can issue a physical card for each employee or each team. You can also issue virtual cards for online payments and subscriptions. You can set different limits for each card.
From the administration panel, you can track expenses, search for specific expenses and see your ongoing subscriptions — it helps you identify duplicates. Users can attach receipts and information to each transaction for accounting purposes.
The company has issued 1,000 credit cards and has processes 10,000 transactions so far. Right now, its clients include startups and tech companies. But Moss expects to expand to other industries soon thanks to today’s funding round.
Moss competes with Spendesk, Revolut Business and others. These corporate card products focus on debit cards. Let’s see if offering credit cards turns out to be an important differentiating feature.
Source: https://techcrunch.com/2021/01/15/corporate-credit-card-platform-moss-raises-25-5-million/
The European Medical Agency (EMA) has warned that information on COVID-19-related medicines and vaccines, which was stolen in a cyber attack last December and leaked online earlier this week, includes correspondence that’s been manipulated prior to publication “in a way which could undermine trust in vaccines”.
It’s not clear exactly how the information — which includes schematics of drug structures and correspondence relating to evaluation processes for COVID-19 vaccines — has been doctored.
We’ve reached out to the agency with questions.
One security researcher, Lukasz Olejnik, who has raised concerns about the leak via Twitter suggested the doctored data will be “perfect for sowing distrust” because the biotechnical language involved in the leaked correspondence will not be widely accessible.
Now I understand why this data is perfect for sowing distrust. (disinformation). The documents are extremely hermetic, using niche biotech-technical language. No layperson is able to understand this. Perfect for conspiracy thinking, because it does have the numbers-percents. https://t.co/e0qfYoV3R0
— Lukasz Olejnik (@lukOlejnik) January 15, 2021
Equally, it also seems possible that the high bar of expertise required to properly parse the data could limit how much damage the manipulated versions can do by limiting their viral appeal.
But it’s notable the EMA has raised concerns over the risk to trust in coronavirus vaccines.
“Two EU marketing authorisations for COVID-19 vaccines have been granted at the end of December/beginning of January following an independent scientific assessment,” the EMA writes in the latest update on the hack.
“Amid the high infection rate in the EU, there is an urgent public health need to make vaccines available to EU citizens as soon as possible. Despite this urgency, there has always been consensus across the EU not to compromise the high-quality standards and to base any recommendation on the strength of the scientific evidence on a vaccine’s safety, quality and efficacy, and nothing else.
“EMA is in constant dialogue with the EC, and other regulators across the network and internationally. Authorisations are granted when the evidence shows convincingly that the benefits of vaccination are greater than any risks of the vaccine. Full details of the scientific assessments are publicly available in the European Public Assessment Reports on EMA’s website,” it adds.
At the time of writing a criminal investigation into the cyber attack remains ongoing.
The attack has not been attributed to a specific hacking group or state actor and there’s no confirmation of who is responsible for trying to sew coronavirus-related disinformation by seeding doctored medical documents online.
However, last November Microsoft warned that hackers backed by Russia and North Korea had targeted pharmaceutical companies involved in the COVID-19 vaccine development efforts.
Back in June, the European Commission also raised concerns about the risks of coronavirus vaccine disinformation spreading in the coming months — simultaneously name-checking China and Russia as foreign entities it said it had confirmed as being behind state-backed disinformation campaigns targeting the region.
So suspicion seems likely to fall on the usual ‘hostile suspect’ states.
We’ve seen similar ‘doctored leak’ tactics attributed to Russia before — typically related to attempts to interfere with elections by smearing candidates for high political office.
Researchers have suggested that the hackers responsible for the 2015-16 breaches of the Democratic National Committee’s network snuck doctored data into the leaked emails — an attack that was subsequently attributed to Russia.
While, more recently, there was the infamous ‘Hunter Biden’ laptop incident — which supporters of president Trump sought to leverage against his challenger for the White House (now president-elect) in last year’s presidential race.
In that case, any disinformation punch fizzled out amid a raft of dubious claims around the finding and timing of the claimed data cache (along with much greater general awareness about the risk of digital fake smear tactics in political campaigns in the wake of revelations about the scale of Russia’s social media influence disops in the 2016 US presidential election).
In an earlier incident, from 2017, emails linked to the French president Emmanuel Macron’s election campaign also leaked online shortly before the vote — coinciding with a document dump on an Internet forum that suggested the presidential frontrunner had a secret bank account in the Cayman Islands. A claim Macron’s political movement said was fake.
While in 2019 Reddit also linked account activity involving the leak and amplification of sensitive UK-US trade talks on its platform during the UK election campaign to a suspected Russian political influence operation.
It’s not clear whether that leaked trade dossier had been doctored or not (it was heavily redacted). And it certainly did not deliver a landslide election win to Jeremy Corbyn’s Labour Party — which used the leaked data in its campaign. But a similar, earlier operation which was also attributed to Russia had involved the leak of fake documents on multiple online platforms. (That disinformation operation was identified and taken down by Facebook in May 2019.)
The emergence of leaks of doctored medical data linked to COVID-19 vaccines and treatments looks like a troubling evolution of hostile cyber disops which seek to weaponize false data to generate unhelpful outcomes for others — as there’s a direct risk to public health if trust in vaccine programs are undermined.
There have been state level hacks targeting medical data before too — albeit without the pandemic-related backdrop of an ongoing public health emergency.
Back in 2016, for example, the World Anti-Doping Agency confirmed that confidential medical data related to the Olympic drug tests of a number of athletes had been leaked by the Russia-linked cyber hacking group, ‘Fancy Bear’. In that case there were no reports of the data being doctored.





















































































